What is Smishing? A Comprehensive Guide

We may earn a small fee from the companies mentioned in this post.
As technology advances, so do the methods used by cybercriminals. One such emerging threat is smishing, which targets our mobile devices in increasingly sophisticated ways. But what is smishing, and how can we protect ourselves from falling victim to it?
In this comprehensive guide, we’ll explore the intricacies of smishing, its mechanics, how to identify and recognise smishing messages, common scams, and the best practices for preventing and protecting against these malicious attacks.
Let’s dive in and learn how to keep our personal and financial information secure in the face of this growing menace.
Short summary
Smishing is a form of cybercrime that utilises deceptive text messages to steal sensitive information.
Malicious links and websites are often used in smishing attacks, so it is important to be cautious with suspicious links and unfamiliar websites.
To prevent against smishing attacks, remain vigilant, avoid clicking on suspicious links, employ two-factor authentication & increase awareness.
Understanding Smishing: A definition

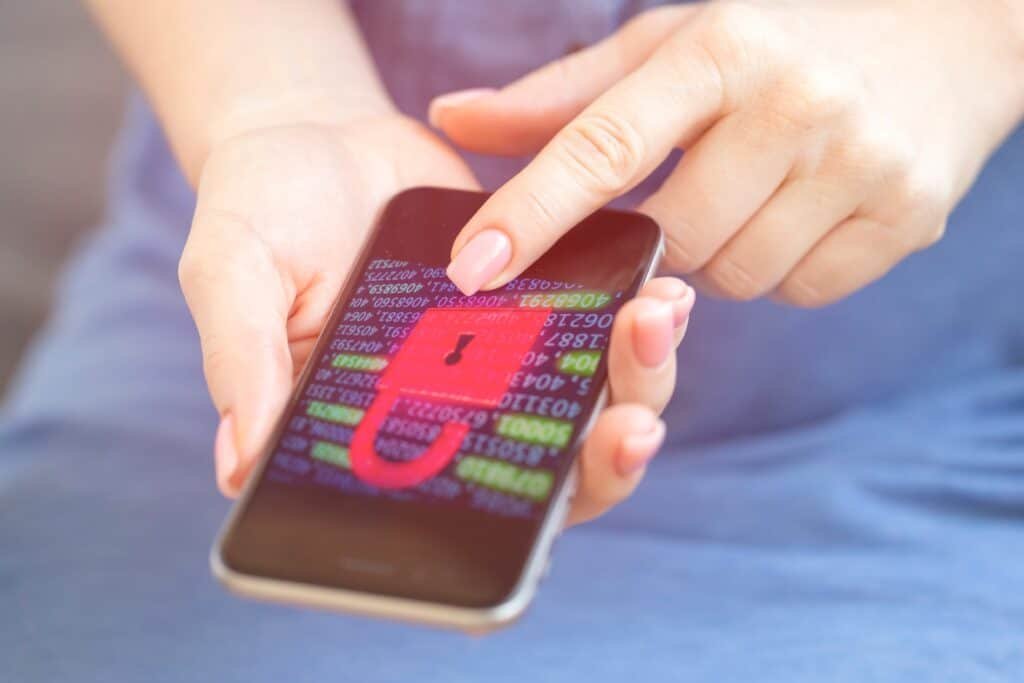
How does smishing work? It’s a form of cybercrime, also known as SMS phishing, that exploits deceptive text messages to deceive individuals into revealing sensitive personal or financial information or installing malicious software on their devices.
The primary aim of smishing is to either trick victims or individuals into providing confidential data that can be used for identity theft, financial theft, or other illicit activities.
With the widespread use of short message service as a form of communication, smishing has become an increasingly prevalent cybersecurity threat.
The mechanics of smishing attacks
At the heart of smishing attacks (which is a form of phishing), lie deceptive text messages and links to malicious websites. These messages often appear to be from legitimate sources, such as financial institutions, government agencies, or well-known companies, that are carefully crafted to deceive victims into providing sensitive information or clicking on malicious links.
The consequences of falling for a smishing attack can be severe, potentially leading to identity theft, financial fraud, or other malicious activities. To combat smishing, it is important to understand its mechanics, be aware of the warning signs, and adopt robust security measures to protect against this ever-evolving threat.
Checkout our informative article on Royal Mail scams
Deceptive text messages
Deceptive text messages(smishing), are fraudulent or malicious text messages designed to manipulate and exploit unsuspecting individuals. Scammers use these messages to extract sensitive personal information, such as passwords, credit card numbers, or bank account information, from victims.
These messages often appear as legitimate communications from trusted sources but contain language that is urgent or demands immediate action.
To protect against smishing attacks, it is crucial to be mindful of the warning signs of a smishing message and never click on links or divulge personal information in response to a suspicious text message. Keeping devices and software up-to-date can also help defend against smishing attacks.
Malicious links and websites
In addition to deceptive text messages, smishing attacks often rely on malicious links and websites to ensnare victims. These links and websites are designed to deceive users, persuading them to divulge personal information or download malware on to their devices.
Clicking on a malicious link can lead to a fraudulent website where the victim is prompted to provide their banking information, enabling the attacker to gain access to the victim’s bank account details and steal their funds.
To minimise the risk of falling prey to such attacks, it is essential to exercise caution and avoid clicking on dubious links or visiting unfamiliar websites. If you suspect that you’ve clicked on a malicious link or visited a malicious website, contact your bank or financial institution immediately and change your passwords.
Checkout our informative article on the Immediate Connect Scam
Identifying and recognising Smishing messages

Recognising smishing messages can be challenging, but there are certain telltale signs to look out for. Verifying the sender’s phone number, noting any grammatical errors, and identifying visual inconsistencies in the message can help you distinguish genuine communications from smishing attempts.
Smishing messages, also known as smishing text messages, may appear to be from a credible source, such as a bank or other financial institution, and may contain language that is pressing or requests for immediate action. Therefore, it is essential to be watchful and prudent when receiving text message, particularly from senders that are unfamiliar or suspicious.
Common types of Smishing scams

Smishing scams come in various forms and can target individuals in different ways. Some common types of smishing scams include:
Impersonation scams
Tech support scams
Account suspension scams
Missed delivery scams
Prize/lottery scams
Charity scams
Malware link scams
Impersonation scams involve attackers posing as well-known organisations or individuals, such as banks, government agencies, or reputable companies, to request personal information in order to gain the trust of their victims.
Tech support scams, on the other hand, involve attackers pretending to be representatives from tech companies, claiming that the victim’s device or account has been compromised and that they require sensitive data to resolve the issue.
Messages claiming that an account has been suspended are part of account suspension scams. These scam messages prompt the victim to provide sensitive information to verify their identity. Missed delivery scams involve perpetrators sending communications that in messages claim that the recipient has not received a package delivery, and they are required to supply personal information or a payment to rearrange the delivery.
Prize or lottery scams falsely inform victims that they have won a prize or lottery, and require them to provide personal details or make a payment to claim the purported winnings. Charity scams involve unscrupulous individuals falsely representing themselves as legitimate charitable organisations and soliciting donations, often after a major event or during the holiday season.
Malware link scams involve messages containing a link that, when clicked, installs malicious software on the victim’s device, allowing the attacker to access confidential information or gain control over the device.
Checkout our informative article on what a cyber attack means
Preventing and protecting against smishing attacks

To protect against smishing attacks, it is vital to:
Remain vigilant of unsolicited messages
Avoid clicking on links in unexpected or unsolicited text messages
Confirm the sender’s identity through reliable communication channels
Deploy security software, such as McAfee Mobile Security, to help safeguard against smishing attacks.
In addition to these measures, it is important to:
Increase awareness about smishing attacks
Educate ourselves and others about the warning signs and best practices for defence
Employ two-factor authentication for online accounts to add an extra layer of security, making it more difficult for attackers to gain access to your personal information.
If you suspect a smishing attempt, do not respond to the message. Report it to your mobile carrier by forwarding the message to 7726 (SPAM).
7726 is a number that most mobile customers using UK networks can text to report unwanted SMS messages or phone calls on a mobile. The number ‘7726’ was chosen because it spells ‘SPAM’ on an alphanumeric phone keypad – that’s a handy way of remembering it.
Taking these proactive steps can significantly reduce the likelihood of falling victim to smishing attacks and help protect our sensitive information from cybercriminals.
What to do if you fall victim to smishing

If you suspect that you’ve fallen victim to a smishing attack, it’s important to act quickly. Here’s what you should do:
Do not click on any links in the suspicious message.
Verify the message source by contacting the supposed sender through reliable channels.
Report the smishing attempt to your mobile carrier by forwarding the message to 7726 (SPAM).
After reporting the smishing attempt, take the necessary steps to secure your personal information and other personal data. Here’s what you should do:
Change your passwords.
Monitor your accounts for suspicious activity.
Contact your bank or financial institution if you believe your financial information has been compromised.
By acting swiftly and diligently, you can minimise the potential damage caused by a smishing attack.
Checkout our infirmative article on best practise tips for smart phone security
The rise of Smishing and its impact on mobile security
The growing prevalence of smishing highlights the importance of mobile security in today’s interconnected world. As we increasingly rely on our mobile devices for communication, banking, and accessing sensitive information, it becomes crucial to protect ourselves from smishing and other online threats via mobile phone.
The rise of smishing underscores the need for increased awareness and protection against this growing threat. By understanding the mechanics of how smishing attacks work, identifying and recognising smishing messages, and adopting robust security measures, we can shield our personal and financial information from cybercriminals and maintain a secure mobile experience in the face of evolving threats.
Summary
In conclusion, smishing is a growing and insidious threat to our mobile security. It is essential to understand the mechanics of smishing attacks, recognise the warning signs, and adopt robust security measures to protect our sensitive information.
By remaining vigilant, educating ourselves, and taking proactive steps to safeguard against these types of smishing attacks, we can navigate the digital world with confidence and help thwart the efforts of cybercriminals.
Frequently Asked Questions
What is smishing
Smishing is a type of phishing attack where attackers use SMS messages to deceive recipients into providing personal information, such as passwords or credit card numbers. It often involves a text message containing a link or phone number that directs the victim to a fraudulent website or prompts them to call a fake customer service number.
What is an example of smishing?
An example of a smishing scam is receiving an SMS requesting personal data such as usernames or passwords that pretends to be from a bank or other authoritative source
What is the difference between smishing vs phishing?
Smishing attacks are cybercrimes that use text messages to trick users into revealing data, while phishing attacks occur through email, with the goal of stealing personal information such as login credentials, bank statements or credit card numbers.
How can I recognise a smishing message?
Verify the text messaging sender’s phone number, look for grammar errors, and be aware of visual discrepancies to recognise smishing messages.
What are some common types of smishing scams?
Common smishing scams include impersonation, tech support, account suspension, missed delivery, prize/lottery, charity and malware link scams.
How can I protect myself from smishing attacks?
Be cautious of unsolicited messages, avoid clicking on links, confirm the sender, deploy security software, increase awareness, use two-factor authentication, don’t respond, and report any smishing attempts to stay protected from smishing attacks.
Useful reference websites
- Action Fraud – www.actionfraud.police.uk
- The UK’s national reporting center for fraud and cybercrime, offering detailed information on various scams, including smishing.
- The National Cyber Security Centre (NCSC) – www.ncsc.gov.uk
- The NCSC offers expert guidance on cyber security, including information on smishing and how individuals and organisations can safeguard against it.
- Which? Consumer Rights – www.which.co.uk
- Which? provides consumer advice and has specific articles on smishing, explaining how these scams work and how to report them.
- The Information Commissioner’s Office (ICO) – www.ico.org.uk
- The ICO is the UK’s independent authority set up to uphold information rights. They provide guidance on unwanted marketing, including smishing, and how to report it.
With over three decades of experience in the heart of London’s financial sector, I have dedicated my career to the pursuit of robust cybersecurity practices and IT leadership. As a Certified Information Systems Security Professional (CISSP), Certified Information Security Manager (CISM), Certified Chief Information Security Officer (C|CISO), Certified Ethical Hacker (CEH), and Computer Hacking Forensic Investigator (CHFI), I bring a wealth of knowledge and expertise to the table.
My journey in the field of cybersecurity has not only been about personal growth but also about sharing my insights with others. As an international speaker, I have had the privilege of addressing audiences worldwide, discussing the importance of cybersecurity in today’s digital age. My passion for knowledge sharing extends to my work as an author and blogger, where I delve into the complexities of cybersecurity, offering practical advice and thought leadership.
In my role as a CISO and Head of IT, I have overseen the development and implementation of comprehensive information security and IT strategies. My focus has always been on creating resilient systems capable of withstanding the evolving landscape of cyber threats.
My Master’s degree in Cybersecurity has provided a solid academic foundation, which, when combined with my practical experience, allows me to approach cybersecurity from a holistic perspective.
I am always open to connecting with other professionals in the field, sharing knowledge, and exploring new opportunities. Let’s secure the digital world together.

