What is Two Factor Authentication (2FA) and How Does It Work?

We may earn a small fee from the companies mentioned in this post.
In an age where cyber threats are ever-evolving, it’s crucial to protect our digital identities and valuable information. “What is two factor authentication?” you may ask. Two-Factor Authentication (2FA) has emerged as a powerful tool in the fight against unauthorised access, providing an additional layer of security beyond traditional passwords.
In this article, we will explore the world of 2FA, diving into various methods, their strengths and weaknesses, and how to implement them across different platforms. Join us as we venture into the realm of enhanced account security and take a glimpse into the future of user authentication with the answer to “what is two factor authentication?”
Short Summary – What is Two Factor authentication
Two-Factor Authentication (2FA) is a security system requiring two forms of identification to access online accounts.
Possession factors, knowledge factors and inherence factors are all authentication methods used for 2FA.
Additional measures such as password managers, VPNs and multi-factor authentication can Strengthen digital security.
Understanding Two-Factor Authentication (2FA)

Two-Factor Authentication (2FA) is a security measure that requires users to the same password and provide two distinct forms of identification to access their online accounts. By adding this extra layer of protection, 2FA ensures that even if a hacker manages to crack your password, they still can’t gain unauthorized access to your account without the second authentication factor.
From knowledge factors like passwords to possession factors like smartphones, and inherence factors like biometrics, 2FA offers a more robust security solution to counteract the ever-growing cyber threats we face today.
The Need for Enhanced Security
The increasing prevalence of cybercrime and the inherent weaknesses of single-factor authentication methods such as passwords have made it abundantly clear that we need enhanced security to protect our online accounts. With billions of user records leaked in data breaches in recent years, it’s no surprise that hackers are constantly devising new ways to gain unauthorized access to our sensitive information.
Two-Factor Authentication (2FA) addresses this growing concern by adding an extra layer of security to the authentication process. By requiring users to provide two different authentication factors, 2FA makes it significantly more difficult for attackers to gain access to your account, even if they have your password.
By upgrading your account security with 2FA, you are taking a significant step towards keeping your sensitive data safe from the prying eyes of cybercriminals.
You may find our article on best practice tips for smart device security
How 2FA Works
At its core, 2FA is a simple yet powerful concept that involves providing two different authentication factors to verify a user’s identity and grant access to an account. These factors can be broadly categorized into three types: knowledge factors (something you know), possession factors (something you have), and inherence factors (something you are). Popular 2FA methods include SMS-based 2FA, authenticator apps, and hardware security keys. SMS-based 2FA sends a one-time passcode to the user’s mobile phone, the verification code while authenticator apps generate time-based passcodes on the user’s device. Hardware security keys, on the other hand, require the user to physically possess a security token that generates a unique code for authentication.
While 2FA offers an additional layer of security, it’s essential to be aware of potential risks associated with different 2FA methods. For instance, SMS-based 2FA can be vulnerable to interception or SIM swapping, while biometric authentication factors, like fingerprints, can’t be changed if they are leaked or replicated. Nevertheless, when implemented correctly, 2FA is a powerful tool in your digital security arsenal.
Types of Authentication Factors
In the world of 2FA, there are three primary types of authentication factors: knowledge, possession, and inherence. Each of these factors plays a vital role in creating a more secure and robust authentication process. By combining different factors, 2FA ensures that even if one factor is compromised, the attacker still can’t gain access to your account without the other two factor authentication secure another factor.
Let’s delve deeper into each of these factors and understand their significance in the realm of 2FA.
Knowledge Factors
Knowledge factors or knowledge factor may involve information that only the user knows, such as passwords, PINs, or security questions. These factors are typically the first line of defense in the authentication process, as they require the user to provide a piece of information unique to them. Although knowledge factors are essential in user authentication, relying solely on them can be risky, as attackers can use various methods to obtain this information.
That’s where the other 2FA factors come into play, providing a much-needed additional layer of security.
Possession Factors
Possession factors require the user to have a specific item, like a mobile device, hardware token, or security key, to authenticate their identity. These factors add an extra layer of security, as attackers would need physical access to the user’s possession factor to gain unauthorized access to the account. One common example of a users authenticating their possession factor is receiving a push notification on a mobile device for authentication purposes.
While possession factors offer a more secure authentication method, they can also be prone to theft or loss, making it crucial to keep your possession factor safe and secure.
Inherence Factors
Inherence factors are unique to the user and involve biometric data, such as fingerprints, facial recognition, or voice patterns. These factors are considered more secure than other authentication factors, as they are difficult to replicate and require the physical presence of the user.
However, inherence factors are not without their potential drawbacks. For example, if a user’s biometric data is compromised, it can’t be changed like a password or replaced like a hardware token. Nevertheless, when used in conjunction with other factors, inherence factors can significantly enhance account security.
Check out our informative blog on the 7 types of cyber security threats
Popular Two-Factor Authentication Methods

Now that we’ve explored the different types of authentication factors, let’s take a closer look at some popular 2FA methods that employ these factors. From SMS-based 2FA and authenticator apps to hardware security keys, each of these methods offers its own unique advantages and disadvantages.
Understanding their nuances will help you choose the most suitable method for your needs and ensure a more secure online experience.
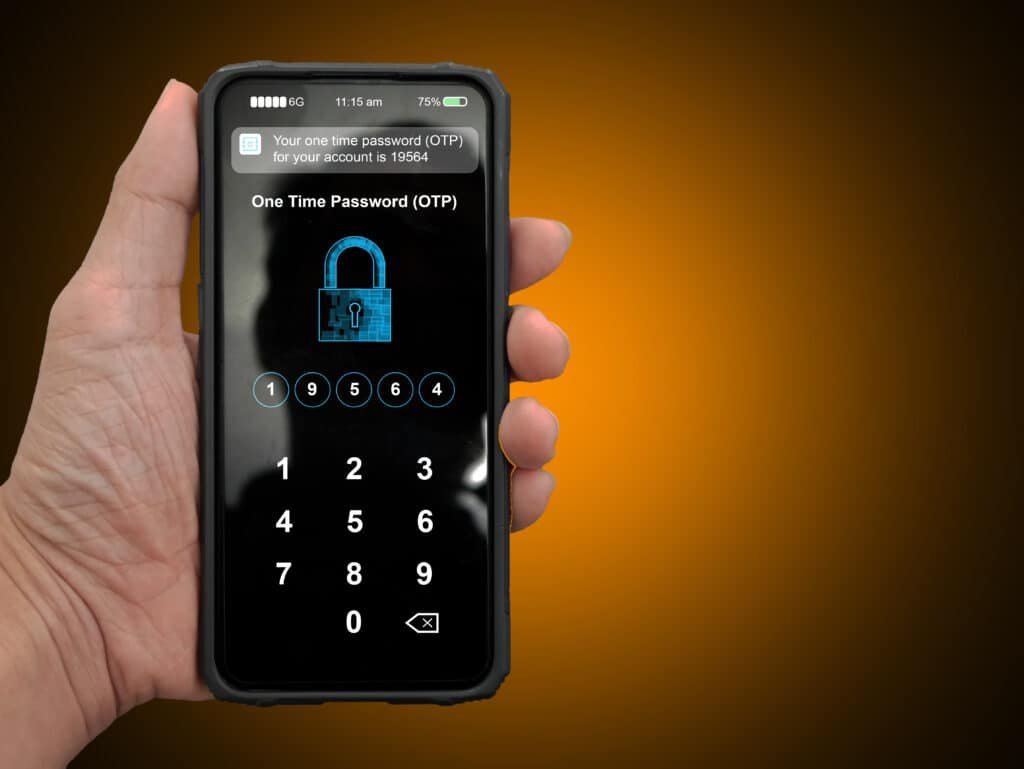
SMS-Based 2FA
SMS-based 2FA involves sending a one-time passcode (OTP) via text message to the user’s mobile phone. While this method is relatively easy to implement and widely used, it comes with potential security concerns. For instance, hackers can intercept SMS messages or perform SIM swapping attacks to gain access to the OTP, compromising the security of the 2FA process.
Despite these risks, SMS-based 2FA is still more secure than relying solely on a password. However, it’s essential to be aware of its potential vulnerabilities and consider using alternative 2FA methods, such as authenticator apps or hardware security keys, for a more secure authentication experience.
Authenticator Apps
Authenticator apps, such as Google Authenticator, generate time-based passcodes on the user’s device for authentication purposes. Unlike SMS-based 2FA, authenticator apps do not rely on text messages, making them less susceptible to interception or SIM swapping attacks. Furthermore, these apps offer a more convenient experience, as users don’t need to wait for an SMS message to arrive and can access their passcodes even in areas with poor network coverage.
In addition to their increased security and convenience, authenticator apps also provide users with more control over their 2FA process, as the passcodes are generated locally on their mobile devices. This makes authenticator apps an attractive option for those seeking a more secure and user-friendly 2FA method.
Hardware Security Keys
Hardware security keys provide a physical security key for authentication, offering high security but may be less convenient due to the need to carry the key at all times. These devices generate unique cryptographic codes used to confirm the authentication request and user’s identity during the login process.
While hardware security keys are considered one of the most secure 2FA methods, they come with their own set of drawbacks. For instance, users must have the key with them to access their accounts, which can be inconvenient, and losing the key can make account recovery challenging. Nevertheless, for those who prioritize security over convenience, hardware security keys can be an excellent choice for 2FA.
Implementing Two-Factor Authentication

Now that we have a solid understanding of 2FA and its various methods let’s explore how to implement it on different platforms. Whether it’s your social media accounts, email providers, or e-commerce websites, activating 2FA can significantly enhance your account security and protect you from unauthorized access.
In this section, we’ll guide you through the process of setting up 2FA on various platforms to help you stay secure in the digital world.
Setting Up 2FA on Social Media
Implementing 2FA on social media platforms like Facebook and Twitter is a crucial step in securing your online presence. With the vast amount of personal information stored on these platforms, unauthorized access can have severe consequences, including identity theft and financial loss.
To set up 2FA on social media, you’ll typically need to access the security settings of your account and enable the two-factor authentication feature. Most platforms offer various 2FA methods, such as SMS-based 2FA, authenticator apps, or hardware security keys, allowing you to choose the one that best suits your needs and preferences.
Enabling 2FA on Email Providers
Email accounts are often the gateway to a plethora of other online accounts, making them a prime target for hackers. To safeguard your email and the sensitive information it may contain, it’s essential to enable 2FA on multiple accounts, especially email providers like Gmail and Outlook.
Setting up 2FA on your email account is typically a straightforward process. You’ll need to access your email provider’s security settings and enable the two-factor authentication option. Like social media platforms, email providers usually offer a variety of 2FA methods, such as SMS-based 2FA, authenticator apps, or hardware security keys, allowing you to choose the most suitable method for your needs.
Activating 2FA on E-commerce Websites
Online shopping has become an integral part of our lives, and with that comes the need to protect our online account and sensitive financial information on e-commerce websites. Activating 2FA on websites like Amazon and eBay is a crucial step in ensuring the security of your accounts and preventing unauthorized access.
To activate 2FA on e-commerce websites, log into your account and navigate to the security settings. From there, enable the two-factor authentication feature. Most e-commerce websites provide multiple 2FA methods, such as SMS-based 2FA, authenticator apps, or hardware security keys, allowing you to choose the one that best fits your needs and preferences.
Is Two-Factor Authentication Foolproof?

While 2FA provides an additional layer of security, it is important to recognize that it is not entirely foolproof. Potential weaknesses may exist in different 2FA methods, making it essential to stay informed about security risks and best practices.
In this section, we’ll discuss potential vulnerabilities in 2FA and explore additional security measures that can further enhance your account security.
Checkout our article on what is Smishing
Potential Weaknesses in 2FA

No security or operating system ever is perfect, and 2FA is no exception. Potential weaknesses may arise depending on the 2FA method employed. For instance, SMS-based 2FA is vulnerable to intercept or SIM swapping attacks, while hardware tokens can be compromised and easily misplaced.
To mitigate these risks, it’s essential to stay informed about potential security vulnerabilities and choose the 2FA method that best suits your needs and threat model. Moreover, incorporating additional security measures, such as strong, unique passwords and monitoring for data breaches, can help further strengthen account security and protect against potential weaknesses in 2FA authentication code.
Additional Security Measures
Supplementing 2FA with additional security measures can further enhance your account security and mitigate potential vulnerabilities. Some of these measures include using a password manager to generate and store strong, unique passwords, establishing a secure connection through a VPN, and enabling two-step verification on your accounts.
By implementing these additional security measures alongside 2FA, you can create a more robust and secure authentication process, further protecting your accounts from unauthorized access and cyber threats. Remember, the key to staying secure online is to be proactive and vigilant in safeguarding your digital identity.
The Future of User Authentication

As technology advances and the landscape of cyber threats continues to evolve, so too must our approach to user authentication. The future of user authentication may involve innovative methods of authentication requests such as passwordless authentication and multi-factor authentication (MFA), offering even greater security and convenience.
In this section, we’ll explore these exciting developments and their potential impact on the world of user authentication.
Passwordless Authentication
Passwordless authentication methods aim to eliminate the need for traditional passwords, offering a more secure and convenient user experience. By relying on alternative factors for authentication attempt such as biometrics or secure protocols, passwordless authentication reduces the risk of password-based attacks, such as phishing or brute force attempts.
As passwordless authentication becomes more widespread, users can look forward to a future where they no longer need to remember or manage multiple passwords for their accounts. Instead, they can rely on more secure and user-friendly authentication methods that better protect their digital identities and keep their sensitive information safe.
Multi-Factor Authentication (MFA)
Multi-Factor Authentication (MFA) takes the concept of 2FA one step further, requiring three or more authentication factors for even greater security. By combining multiple factors, such as knowledge, possession, and inherence, MFA offers a more robust authentication and security process that is better equipped to adapt to the evolving landscape of cyber threats.
As we move towards a future where MFA becomes the norm, users can expect even higher levels of security for their accounts. This will help to better safeguard our digital identities and ensure that we can navigate the online world with confidence and peace of mind.
Summary
In conclusion, Two-Factor Authentication (2FA) is a powerful tool that adds an additional layer of security to your online accounts, helping to protect your digital identity and sensitive information from unauthorized access.
By understanding the various 2FA methods, their strengths and weaknesses, and implementing them on different platforms, you can take a proactive approach to safeguarding your digital world.
As we look ahead to the future of user authentication, innovations such as passwordless authentication and multi-factor authentication promise to further enhance account security, allowing us to navigate the digital landscape with confidence and peace of mind.
Frequently Asked Questions
What is 2 factor authentication and how does it work?
Two-Factor Authentication (2FA) is a security system that provides an additional layer of protection to your accounts, by requiring two distinct forms of personal identification number such as a password and a code sent to your smartphone or biometrics.
This extra layer of security helps to protect your accounts from unauthorized access, as it requires two forms of authentication to gain access. It also helps to reduce the risk of identity theft, as it requires two forms of authentication to gain access. Additionally, it can help reduce the risk of phishing attacks, as it can help reduce the risk of phishing attacks.
What is an example of 2 factor authentication?
Two-factor authentication is a security measure that requires users to provide two different types of authentication, such as a password and a one-time code sent to a mobile phone or a hardware token, in order to access an account. This method of security has been used for decades and can be used to protect online accounts such as email, social media, and banking.
Two-factor authentication is an important tool for protecting online accounts. It adds an extra layer of security user passwords, making it more difficult for hackers to gain access to sensitive information. It also helps to protect users from phishing attacks, which are attempts to trick users into revealing their passwords or other sensitive information.
How do you set up two-factor authentication?
Set up two-factor authentication by accessing your privacy settings on your mobile app, selecting Security and Login, and enabling 2-Step Verification.
Then follow the on-screen steps to complete the setup.
What are the three types of authentication factors used in 2FA?
Two-Factor Authentication (2FA) uses three authentication factors: knowledge (e.g. passwords), possession (e.g. smartphones or hardware tokens) and inherence (e.g. biometrics like fingerprints or facial recognition).
Knowledge factors are typically passwords or PINs that the user must remember. Possession factors are items that the user must have with them, such as a smartphone or hardware token. Inherence factors are biometric characteristics that are unique to the user, such as fingerprints or facial recognition.
What are some popular 2FA methods?
Popular 2FA methods include SMS-based 2FA, authenticator apps, and hardware security keys, ensuring users’ accounts login credentials are kept secure and protected.
These methods provide an extra layer of security, making it difficult for hackers to gain access to user accounts. They also help to protect users from phishing attacks, which are becoming increasingly common. 2FA is an important security measure.
Two-Factor Authentication Facebook
When you enable 2FA on Facebook, every time you log in from a new device or browser, you’ll be prompted to enter a unique code that’s sent to your chosen verification method.
Facebook provides several options for the second authentication factor, including text messages, authentication apps like Google Authenticator, or a physical security key.
By setting up 2FA, you add a robust security measure that significantly enhances the protection of your Facebook account against unauthorised access and potential hacking attempts.
External Reference Information
- National Cyber Security Centre (NCSC) – Multi-factor authentication for online services: This guidance from the UK’s NCSC describes how to use multi-factor authentication (including two-factor authentication) to protect against password guessing and theft.
- Get Safe Online – Two-Factor Authentication: Get Safe Online provides a simple explanation of two-factor authentication and why it’s important for online security.
- Barclays – Two-Factor Authentication: Barclays Bank provides information on two-factor authentication, emphasizing its importance in banking security.
These resources cover various aspects of two-factor authentication, including its importance, how to set it up, and specific applications in different contexts like banking and education. They can provide valuable insights and practical guidance for readers interested in enhancing their online security.
With over three decades of experience in the heart of London’s financial sector, I have dedicated my career to the pursuit of robust cybersecurity practices and IT leadership. As a Certified Information Systems Security Professional (CISSP), Certified Information Security Manager (CISM), Certified Chief Information Security Officer (C|CISO), Certified Ethical Hacker (CEH), and Computer Hacking Forensic Investigator (CHFI), I bring a wealth of knowledge and expertise to the table.
My journey in the field of cybersecurity has not only been about personal growth but also about sharing my insights with others. As an international speaker, I have had the privilege of addressing audiences worldwide, discussing the importance of cybersecurity in today’s digital age. My passion for knowledge sharing extends to my work as an author and blogger, where I delve into the complexities of cybersecurity, offering practical advice and thought leadership.
In my role as a CISO and Head of IT, I have overseen the development and implementation of comprehensive information security and IT strategies. My focus has always been on creating resilient systems capable of withstanding the evolving landscape of cyber threats.
My Master’s degree in Cybersecurity has provided a solid academic foundation, which, when combined with my practical experience, allows me to approach cybersecurity from a holistic perspective.
I am always open to connecting with other professionals in the field, sharing knowledge, and exploring new opportunities. Let’s secure the digital world together.

